Computer attack patterns have evolved in recent years. Cryptolockers have become the spearhead of many hackers.
Does your antivirus vendor promise you that you are protected against these new threats? OK, prove it before you get stuck by a real attack.
Let’s talk about cryptolocker
The principle of a cryptolocker is quite simple: encrypt target files (often.doc, .txt, . odt, etc.) and then demand a ransom. A ransomware has nothing to gain by destroying the underlying OS, so system files are rarely touched.
So it will encrypt as many files as possible and then ask for payment (often in Bitcoin or other cryptocurrencies) to obtain the decryption key.
These threats are very serious, large groups have had to face them recently and were sometimes paralyzed for several days.
Detecting a cryptolocker
The concern is that we are nowadays in a world with more and more sophisticated and discreet malware. Nowadays, the power of heuristic engines on antivirus software is widely exploited. These engines detect abnormal or dangerous behavior rather than just a previously identified binary (signature).
The purpose of the test I’m offering today is to test the performance of this engine, whether it’s on its detection speed, reaction (blocking the attack) and its remediation.
Ransomware as a service
To perform these tests, we will use a small open-source tool:
This small python script simulates the basic operation of a cryptolocker.
It will allow you to start a local server, which will be used to collect information about the encryption (IP address, encryption keys, etc.).
It also allows you to create the script that will be used for the encryption, and to compile it to make it portable.
Why is this project interesting?
First of all, the interest is already that it is completely harmless:
- It does not spread on your network
- You can decrypt the data
- It is open source, you can see or modify the code
- it works on all OS, because it only requires Python 3
Then, the attack model is all the more interesting as it is realistic, the use of a python script in a “standalone” mode allows simulating a concrete case: a third party library available on pip for example, which would be malicious.
This also allows you to check that your antivirus software reacts to attacks that are not binaries.
Download and set up the prerequisites
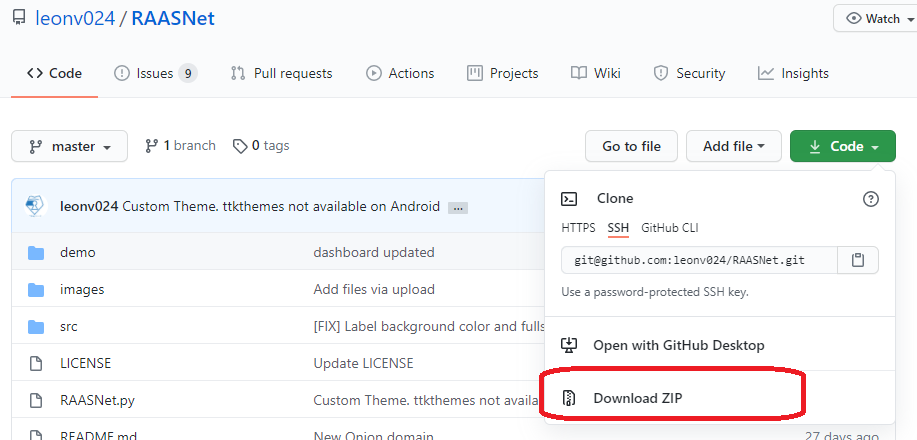
Clone the repository
If you have the Git client installed, you can directly clone the repository via the Git client:
git clone [email protected]:leonv024/RAASNet.git
If you don’t have the Git client, you can also directly download the zip file from the repository.
Installing the prerequisites
On the PC on which you want to test the script, it is necessary to have Python 3 installed, as well as the pip3 client.
For these installations, I invite you to go to the associated documentation pages to see how to install them according to your OS context:
- Python 3: https://docs.python.org/fr/3/using/index.html
- PIP 3: https://pip.pypa.io/en/stable/installing/
Once these steps are made, it is necessary to install the prerequisites:
pip install -r ./requirements.txt
Under Windows, it is necessary to install an additional package for the management of windows:
pip install image
Start the application
Once the prerequisites are installed, you can start the application:
python3 ./RAASNet.py
Once this is done, you will have to create an account, it is not necessary to have a valid email address for this account.
Then you can start the server, this will allow you to collect information when encryption starts.
Warning: If you do not start the server, you will not have the decryption key!
Initiate the attack payload
Now that we have prepared the base of our attack. The next step is to create the attack script.
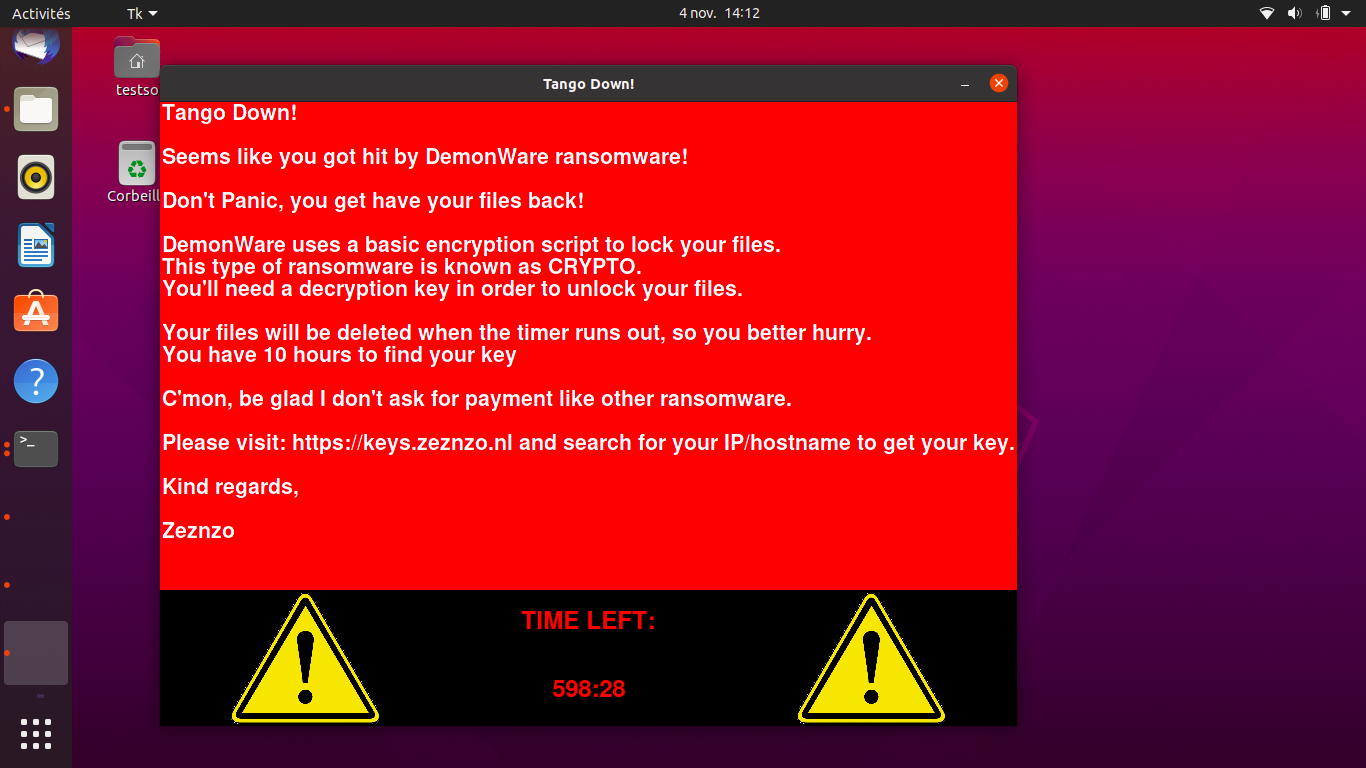
To do this, we will click on “Generate Payload”. Then you can select the options for your attack:
- The list of target files
- The base directory for the attack
- The encryption method to use
- Whether or not to display a window at the end to indicate that the content is encrypted
Once the configuration is done, just click on “Generate” to create two scripts:
- payload.py: this script is your attack load itself
- decrypt.py: this script allows decrypting the files after the attack
It’s popcorn time!
Now that you have everything ready, it’s the most fun part: launching the attack!
Here are three points to watch on your antivirus:
- whether or not the attack is detected
- the speed of detection
- the possibility to remedy or not: does the antivirus know how to restore the encrypted files?
To launch the attack, a simple command:
python3 payload.py
Depending on the encryption method, you have chosen and the volume of data, the encryption will take from a few seconds to several minutes.
The interest here is to see if your antivirus software reacts or not to the encryption, via its heuristic engine.
For the test to be as consistent as possible, don’t hesitate to vary the attack mode, for example by launching the encryption from a USB key and remotely setting up the server.
Moreover, to be sure to trigger your antivirus, don’t hesitate to put a little bit of file volume (a few thousand) to make sure that the volume is sufficient to make it react.
And in binary?
RAASNet also allows you to convert python scripts into classic binaries. Including replacing the basic icon.
By doing so, you can reproduce classic attack patterns, e.g., a PDF invoice by email, an autorun executable on a USB stick, a download from a third-party site, etc.
Once again, the idea is to reproduce classic attacks and observe the reaction (or not) of your antivirus.
To conclude
Whether your antivirus has detected the attack or not, you must remain pragmatic.
Depending on the vector used, it may be normal that your antivirus considered the action as legitimate, that’s why you should not hesitate to transfer the viral load on a simple USB key, for example.
Moreover, this malware is voluntarily unknown and harmless, so the risk is controlled.
However, this is a simple and interesting test to do to check the reaction of your antivirus.
For my part, my personal antivirus detected the abnormal behavior after a few encrypted files and restored the content.