Traefik 2.3 (codename: Picodon - picodon is a cheese, which you can see in the banner of this article) is available as a release candidate since a few days. More than a simple version increment, it brings a lot of new features.
Two big new features caught my attention:
- The new service of Traefik : Traefik Pilot
- Adding plugin management
Another new feature, compatibility with ECS will be covered in a future article.
Is there a pilot in the plane?
Traefik is a complete and powerful reverse proxy, as I already presented in previous articles. Nevertheless, it lacked a healthcheck solution.
It is now possible, for free!
A new service is dedicated to this feature, proposed by Containous (the editor, among others, of Traefik).

This service is called Traefik Pilot, it is for the moment very basic and only requires the healthcheck of your Traefik, allowing you to send a notification if it does not answer anymore. It is available at the url https://pilot.traefik.io/
After a quick registration, it is possible to register a Traefik instance.
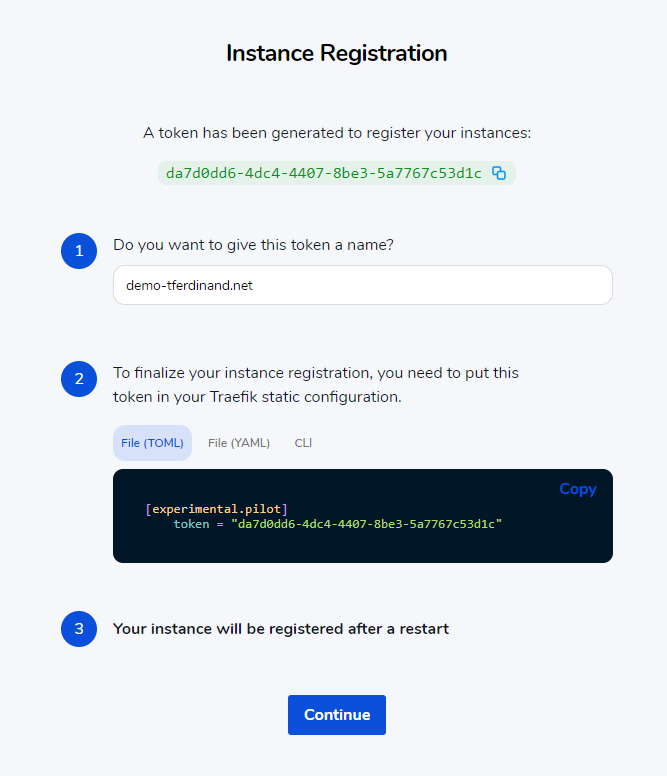
Fake token, you can always copy it ;)
Beware of the token
Contrary to what is indicated on the site, you must copy the token without the quotes around it, otherwise you will get a message telling you that the token is invalid! This bug has been reported to Containous, who, I have no doubt, will fix it quickly!
So I added the command line parameter in the Traefik startup line on Kubernetes.
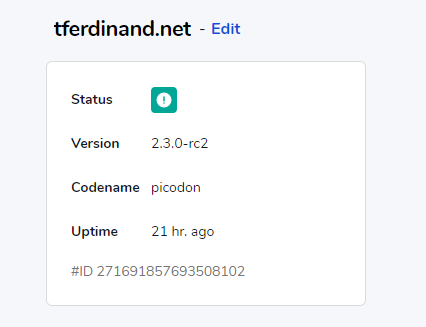
After a reboot, you should see your status change to OK.
However, there are a few things to keep in mind:
- This status currently only corresponds to the status of your Traefik container, and does not mean that the backends are functional.
- This healthcheck is sent from your instance, in “heartbeat” mode, and does not necessarily mean that your server is reachable.
- As the signal is sent in heartbeat, it is also possible to monitor instances in the application area.
It is then possible, by clicking on your name at the top right, to define alarms, via webhooks or by e-mail.
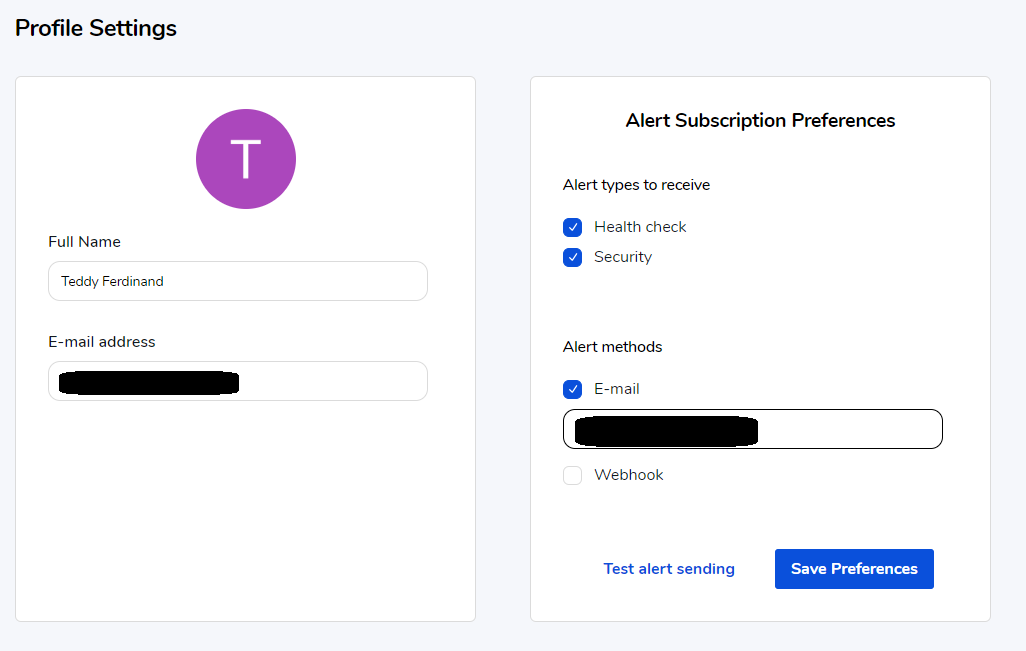
Note that it is possible to indicate that you wish to receive security alarms, linked to the discovery of possible CVE on your version of Traefik.
Warm up the plugins
I used for many years the very popular Apache httpd. One of the enormous strengths of this product is undoubtedly its modularity, allowing the community to extend its functionality.
Traefik now allows the use of plugins as well. The list is currently rather small, but I have no doubt that the catalog will grow quickly!
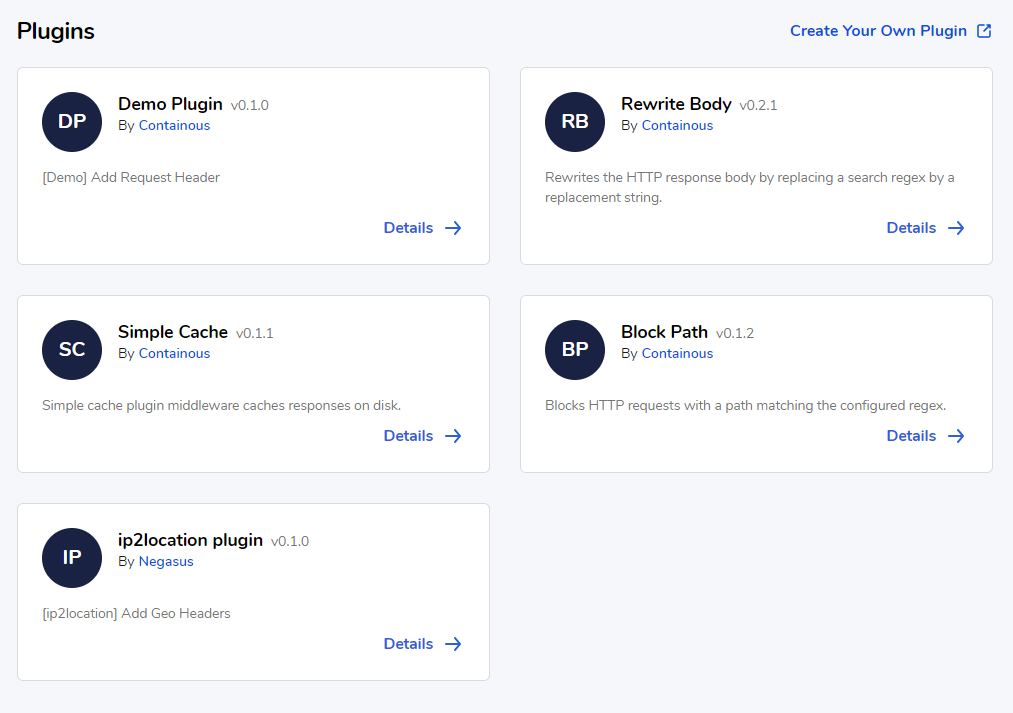
Plugins are written in Go, and it is possible to contribute by following the guide provided by Containous.
For the purpose of this article, I chose the “Block Path” plugin edited by Containous. This plugin allows to dynamically block access to certain pages based on regular expressions.
Blocked pages will directly return a 403 (Forbidden) error.
The interest of this kind of plugins, already existing in most reverse proxies, is to be able to intercept access to certain pages, and thus prevent the backend from receiving any hit.
This allows :
- Not to generate a load (for example in the case of an admin page that could be brute force/DDOS).
- To avoid exposing an undiscovered zero day flaw, since the backend does not receive any requests.
Charger le plugin
The loading of the plugin is done via the static configuration of Traefik. For my part, I loaded it via the command line parameters, since this is how I chose to load my entire configuration.
args:
- --providers.kubernetescrd
- --accesslog=true
- --accesslog.filepath=/var/log/traefik/access.log
- --accesslog.fields.headers.defaultmode=keep
- --entrypoints.web.address=:80
- --entrypoints.websecure.address=:443
- --certificatesresolvers.le.acme.email=myawesomemail@mail.com
- --certificatesresolvers.le.acme.storage=/cert/acme.json
- --certificatesResolvers.le.acme.httpChallenge.entryPoint=web
- --experimental.pilot.token=mytoken
- --experimental.plugins.demo.moduleName=github.com/containous/plugin-blockpath
- --experimental.plugins.demo.version=v0.1.2
You can see line 12 and 13 the loading of the plugin.
In my command line, “demo” is the name I gave to the plugin (used just after). moduleName thus contains the path to the GitHub repository containing the plugin, version being the Git version to checkout.
Once this configuration is done, it is necessary to restart Traefik.
Configuring the plugin
The plugin then behaves like a classic middleware, if you remember my previous articles, middlewares are components that plug between Traefik and your backend, and can alter the normal behavior. For example, on this page, a middleware allows you to define the necessary security headers.
For example, I have declared a new middleware in my Kubernetes :
apiVersion: traefik.containo.us/v1alpha1
kind: Middleware
metadata:
name: demo
spec:
plugin:
demo:
regex: ["^/demo-[a-z]{1,5}"]
So we find, in a classic way:
- Line 4: The name of my middleware, which can be different from the name I gave to my plugin.
- Line 6: I tell Traefik that this middleware is a plugin
- Line 7: I indicate the name I gave to my plugin when I loaded it
- Line 8 and following, if needed: I now indicate the configuration of my middleware.
In my example, I indicated to block any access whose path would start with “/demo-” with 1 to 5 lowercase letters.
Load middleware
Now that I have defined my middleware, I have to load it into my IngressRoute.
So I modify my IngressRoute by indicating to load this middleware too. As a reminder, you can define multiple middlewares on your IngressRoutes which will be executed in a row.
apiVersion: traefik.containo.us/v1alpha1
kind: IngressRoute
metadata:
name: traefik-web-ui-tls
namespace: default
spec:
entryPoints:
- websecure
routes:
- kind: Rule
priority: 1
match: (Host(`www.tferdinand.net`) || Host(`tferdinand.net`)) && PathPrefix(`/`)
services:
- name: ghost-tfe-fr
port: 2368
helthcheck:
path: /
host: tferdinand.net
intervalSeconds: 10
timeoutSeconds: 5
middlewares:
- name: security
- name: demo
tls:
certResolver: le
options:
name: mytlsoption
namespace: default
You can see the load on line 23, which will be executed after adding the security headers.
Let’s test the plugin
Now it’s time to test my plugin
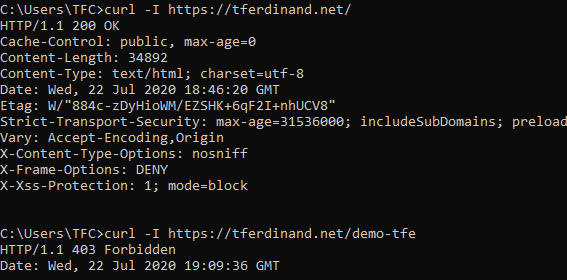
Yes, I also use Windows, and I assume it ;)
You can see that it has the expected behavior, my normal accesses work the same way, the accesses that match the schema I defined are blocked by Traefik directly.
In conclusion: A small step for Containous, a big step for the community.
Adding plugins and Traefik Pilot are clearly previews at the moment, and don’t allow to take full advantage of their potential, however, this open modularity will allow the community to extend the basic features without making Traefik core heavy.
It also allows companies to potentially develop their own private plugins and thus adapt Traefik to their needs.
Pilot is an excellent initiative, and I can’t wait to see how Containous will turn this trial into a top feature!


