A few days ago, Twitter was the target of a hack inviting, via “verified accounts”, users to send BitCoins to receive double the amount. I suggest a small post on what we can learn from this attack, from a computer security point of view.
Disclaimer
The purpose of this article is not to make an umpteenth analysis of this attack, but rather to recall some basic rules of computer security that this attack reminds me of.
A quick reminder of the facts
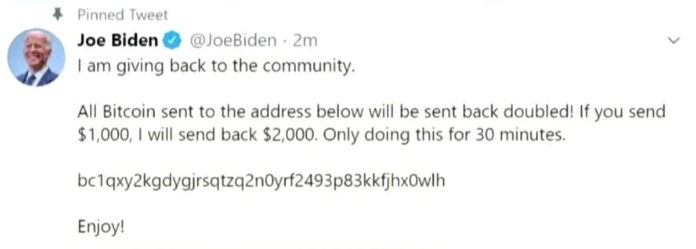
On July 15, 2020, about fifteen “verified” accounts, so with many followers, started sending a message inviting users to send BitCoins to receive double the amount. The message was the same each time:
Among these accounts we have, for example:
- Bill Gates
- Elon Musk
- Joe Biden
- Uber
- Apple
- Jeff Bezos
- Twitter support (to top it off!)
For many hours, users have been sending BitCoins to this wallet.
The last time I looked, the wallet did about 13 BTC (about 120.000$) in about 3 hours! Quite profitable.
To curb the attack as much as possible, Twitter had to disable tweeting for verified accounts for many hours.
The attack vector
The alleged hackers gave an interview to The Times, which you can find here, and the attack vector is almost funny…
It’s mostly an opportunistic attack, myself, I thought it was an organized attack, actually no, it’s almost disappointing… A Twitter employee would have had access to logins and passwords to access the administration interface via messages pinned on a Slack channel… seriously…
It would seem that, despite the attacks Twitter has suffered in the past, security is always the poor relation (like many companies unfortunately).
The attack (or rather attacks)
There were in fact two attacks on the same day, exploiting this “loophole”.
The first one was to be able to use (and thus sell) usernames normally impossible to have, and search for, like “@y” (I don’t understand the interest, but it seems there is one). Some users were obviously willing to pay several hundred dollars for that.
The second attack, we already know about it, it was, for that matter, resounding!
What Twitter says
As I write these lines, Twitter confirms the hack (it would be complicated to say otherwise), confirms that accounts have been compromised, and that the attackers have been able to access email addresses, phone numbers, date of birth, etc… but not passwords, which fortunately are not in clear text in the back office.
In addition, eight accounts had their entire activity downloaded (the equivalent of the data you could have for a RGPD request). These eight accounts are not specified, but Twitter indicates that they would be unverified accounts.
Regarding the attack vector, Twitter indicates that investigations are still ongoing.
In addition, Twitter indicates that hackers would have succeeded in bypassing the MFA, but I remain skeptical at this point.
What I take away from this attack
No business is too big to fall.
As I often say, no company is invulnerable to hackers. In fact, the opposite is often true: the larger the company, the more likely it is to be targeted. Twitter is all the more targeted; indeed, social networks collect the wealth of information on our uses, but also personal information, and even some exchanges that can be sensitive.
Attacks can come from the inside
I often say this, but one of the main flaws in corporate security is that attacks will only come from the outside, but that is not true!
About 2/3 of recent attacks and leaks come from the inside, whether voluntary or not. It is often simpler to compromise the human factor, which is fallible, than antipiracy protections.
Moreover, we could also talk (and I’ve already seen it) about users leaving the company and taking confidential information with them (customer address books, source code, email, etc…), which in itself is an internal leak.
Privileged access is monitored
What shocked me in this attack is the extent of the actions, how an admin user can make so many changes without having, at worst the deterrence to prevent him from chaining too many actions, at best the alerting, in mode “Hey, that’s weird, we have an admin who modifies the email addresses of 30 accounts in a row”.
Administrative rights must be separated a minimum of
In the Twitter admin dashboards that leaked, I was surprised to see that all administration tasks were centralized.
I understand the interest, which is undoubtedly to facilitate the administration work, however, as we’ve seen, if this admin panel is compromised, the radius blast is just huge, giving full power in one access.
Generic accounts should no longer exist
We are in 2020, after the number of hacks that are taking place because of generic credentials that have found their way into the wild, I am still surprised that they are still being used, especially for such sensitive applications.
The generic account is always the wolf in the henhouse, for example, how can we make sure that a user who leaves no longer has his access, that he has not kept the generic account in a corner? How can we make sure that a user is not going to exfiltrate it, share it, or even give it to a colleague while trying to help him out?
It’s very simple, you can’t!
That’s why generic accounts are not allowed.
Logins and passwords are never exchanged on the same media.
Again, this is basic good practice. But in the current case, the attack was all the more simplified as the logins and passwords were co-located. Generally speaking, one should always avoid putting the two pieces of information together, preferably even exchange the password of an encrypted medium, with an automatic expiration.
This is also one of the risks of the full remote
I was talking about teleworking a few weeks ago. Full remote also means allowing much larger IP scopes than just internal. For such a critical application, one will often authorize only certain ranges of internal IPs, or even ideally, specific VLANs corresponding to teams with legitimate access. Therefore, even if I get the logins and passwords, I also have to be able to infiltrate the network, on the right VLAN, which makes the task more complex.
It’s technically possible to do the same thing with VPN. However Twitter announced a few months ago that they were switching to full remote, I think that VPN should be seen as a brake… Moreover in our case the attacker being internal, it is likely that he has VPN access.
The “Nigerian prince scam” has a bright future ahead of it.
What shocks me the most is that people have fallen for this type of attack. This pattern of attack is at least as old as the Internet and yet in 2020, with a population that is normally aware of this type of attack, many people are still falling for it.
I remain skeptical that greed still trumps common sense for some. Personally, from the very first messages, I had categorized it directly as a scam.
We were lucky
We were lucky for this hack; indeed, we came across “novice” hackers who were mostly venal. When we know that a big part of world diplomacy is nowadays played on social networks, it could have been much worse.
Donald Trump announcing a war to any country could, for example, have been credible and created confusion at best, chaos at worst. In the same way, some company announcements could have easily destabilized the world market, which is already in a bad way with CoVid.
Be careful what you store on social networks
This hacks allows me to remind you that everything you send to a site can at one time or another end up in the wild. There has already been the case with some dating sites for example, but also iCloud, Facebook and so on.
Storing data online may be necessary (for example to make back-ups), but it is important to always make sure that they are not usable as they are by encrypting them.
To make a simple analogy, a door will prevent you from entering your home, however, if you leave the key under the mat, it has no real use anymore. When it comes to messaging, when it comes to personal and/or confidential information, prefer end-to-end encryption applications such as Telegram or Signal.
The booty is not so huge
I know you’re going to tell me that they got away with more than $100,000, only you have to face the fact that they now have a lot of people looking for them, for a long time, and given the number of compromised accounts, those who get caught will probably spend many years in the shade. We’ve already seen less “explosive” hacks walk away with far greater gains.
Still, you have to consider that they haven’t dealt all their cards yet, since they have the data for 8 accounts in total, and depending on the accounts and information, there may or may not be a high value (or not).
In conclusion
This attack is unlikely to be the last of this magnitude, however, it is hoped that it will be one of the last with such ease.
Unfortunately, in my daily work of security, I know that the precepts I have described here are often seen as brakes rather than what they are, protections. Safeguards to avoid stupidly bringing down one’s business.
Having already seen proven leaks in companies, which could have had a huge impact, I suspect that it won’t stop tomorrow, simply because many people are not necessarily aware of the dangerousness of what they do, and this is what I have seen every time I have confronted the authors of leaks.
I hope, however, that this event, given the media coverage it has had, will help some users to understand the importance of thinking about safety on a daily basis.

